In today’s digital landscape, software supply chain security stands as a critical priority for organizations aiming to deliver reliable and secure software products. As emerging software security threats intensify and the DevOps risks evolve, companies must navigate a complex web of software vulnerabilities that can jeopardize their operations. Recent insights from JFrog underscore the urgency for businesses to adopt robust strategies to mitigate these AI security concerns alongside the rising frequency of these threats. Security experts emphasize that automating toolchains is no longer a luxury but a necessity, especially as manual processes can lead to vulnerabilities and potential breaches. As organizations increasingly embrace AI-driven innovations, placing a spotlight on software supply chain security will determine their resilience and trustworthiness in this chaotic environment.
When discussing the protection of software development frameworks, it’s essential to consider alternative terms like software lifecycle security and application supply chain safeguards. These concepts highlight the need for continuous oversight and management of both software components and the processes that govern them. With a rapid influx of advanced technologies, organizations face increasing complexities that demand meticulous attention to potential software vulnerabilities and the various risks associated with a dynamic DevOps culture. As security within this domain takes precedence, the deployment of automated toolchain integrations becomes vital, ensuring that businesses remain agile and preemptively tackle AI security concerns. In this interconnected age, securing the entire software production pathway is paramount to fostering innovation without compromising safety.
Understanding Software Supply Chain Security
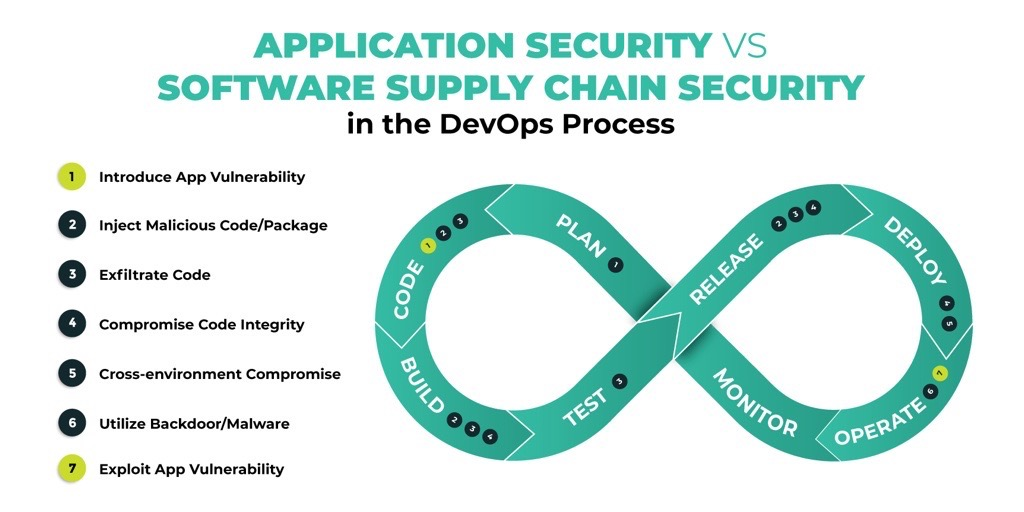
Software supply chain security has emerged as a paramount concern in the era of rapid technological advancement. It encompasses the measures and practices implemented to safeguard the entire process of software development, from coding to deployment. The security of the software supply chain is crucial, as vulnerabilities can be introduced at any stage, potentially compromising the integrity and functionality of software products. As such, organizations need to adopt a holistic approach that encompasses security best practices at every phase of the lifecycle.
Recent revelations regarding software security threats underline the crucial need for robust supply chain security. Companies now face evolving DevOps risks as they navigate the complexities of integrating public machine learning (ML) models into their applications. Without a strong focus on supply chain security, organizations may unknowingly expose themselves to new attack vectors that can exploit weaknesses in their platforms. It is essential to recognize that managing security in the supply chain isn’t just about preventing unauthorized access; it involves continuous monitoring and updating of security protocols to address emergent challenges.
Emerging Software Security Threats
The landscape of software security threats has evolved dramatically in recent years, driven by the increased complexity of software applications and the growing use of third-party components. Malicious packages, which can embed harmful code into legitimate software, are becoming more prevalent. These threats not only compromise individual applications but can also jeopardize entire organizations, leading to significant financial and reputational damage.
Moreover, a staggering increase in exposed secrets and tokens has been reported, showcasing the need for stringent oversight in software development processes. As highlighted by JFrog’s findings, a notable percentage of companies still depend on manual methods for managing their approved ML models, inadvertently increasing their vulnerability to potential breaches. To combat these emerging threats effectively, organizations must invest in comprehensive security measures and automation tools that enable real-time monitoring and response to security incidents.
DevOps Risks and Best Practices
In the fast-paced environment of DevOps, security must be integrated into every stage of the development lifecycle. While organizations strive for agility and speed in delivering software, the risks associated with rapid deployment can lead to significant oversights, especially regarding software vulnerabilities. According to recent studies, a considerable number of organizations do not conduct security scans at both code and binary levels, leaving them susceptible to threats that could be easily identified with effective security measures.
Implementing best practices for DevOps security involves a strategic alignment of development and operations teams to prioritize security from inception. Automating toolchains and incorporating continuous security checks can help mitigate risks throughout the software supply chain. Organizations that enhance collaboration between teams and utilize AI-driven solutions for monitoring and compliance are likely to achieve more robust security outcomes while maintaining the necessary velocity in their development processes.
AI Security Concerns in Modern Development
The rise of artificial intelligence in software development has introduced a new set of security concerns that organizations must address. As companies leverage AI to optimize their development processes, they also face the risk of integrating AI models that may not be fully vetted for security vulnerabilities. The reliance on public ML models can lead to significant exposure if proper security measures are not in place, making it imperative for organizations to adopt proactive strategies to safeguard their AI implementations.
Moreover, as JFrog’s report indicates, a considerable number of organizations still engage in manual efforts to manage access to secure AI models. This manual approach is fraught with risks, as human error can lead to oversights that expose sensitive data and systems to cyber threats. Consequently, companies are urged to automate their governance processes and invest in AI-ready solutions that prioritize security and compliance, ensuring that their innovation-driven development aligns with best practices in security management.
Addressing Software Vulnerabilities in the Supply Chain
Software vulnerabilities pose a significant threat to the integrity of the software supply chain, necessitating a focused effort on identification and mitigation. Recent data shows an alarming increase in new Common Vulnerabilities and Exposures (CVEs), highlighting the importance of ongoing vigilance in security practices. Many organizations fail to adequately assess high-profile CVEs, which could lead to substantial risks if not correctly addressed.
To tackle software vulnerabilities effectively, companies must implement rigorous security scans and validation processes at all levels of their software development. As highlighted by the decreasing percentage of organizations conducting thorough scans, it is evident that many teams need to enhance their security posture. By prioritizing automation and standardized security protocols, organizations can significantly reduce the occurrence of vulnerabilities and leverage real-time data to inform their security strategies.
The Importance of Automation in Toolchains
In the face of increasingly complex software security threats, automation has become a crucial element in enhancing supply chain security. Automation in toolchains facilitates continuous integration and continuous delivery (CI/CD) processes, allowing organizations to perform security checks and validate code at various stages of development. This shift from manual to automated processes not only reduces the risk of human error but also accelerates the overall development lifecycle, enabling organizations to respond swiftly to emerging threats.
Furthermore, automated toolchains can streamline compliance with industry regulations and best practices, ensuring that security protocols are uniformly enforced. Organizations must adopt smart automation solutions that integrate seamlessly with their existing systems, thus creating a cohesive security framework that adapts to the evolving threat landscape. By embracing automation, businesses can stay ahead of potential risks while driving innovation and improving software delivery.
Continuous Monitoring as a Security Strategy
Continuous monitoring is an essential aspect of maintaining software supply chain security. With the ever-evolving landscape of software security threats, organizations cannot afford to rely solely on periodic assessments. Instead, they should implement continuous monitoring strategies that provide real-time visibility into their software environments, identifying vulnerabilities and threats as they arise.
This proactive approach to security enables organizations to quickly remediate issues before they can be exploited by attackers. As highlighted in the findings from JFrog, only a small percentage of IT professionals report their organizations conduct thorough security scans. By prioritizing continuous monitoring, organizations can bolster their defenses and ensure they are not caught off guard by new threats, ultimately leading to a more resilient software supply chain.
Strategies for Secure Software Development
To ensure secure software development, organizations must establish comprehensive strategies that encompass security at every stage of the lifecycle. This begins with integrating security into the planning and design phases, where potential vulnerabilities can be identified and mitigated early on. By fostering a culture of security awareness among development teams, companies can enhance their overall security posture and reduce the risk of vulnerabilities making their way into production environments.
Additionally, utilizing automated tools for code analysis and vulnerability scanning can significantly improve the reliability of software releases. Many organizations have begun adopting DevSecOps practices, which emphasize the importance of collaboration between security, development, and operations teams. By working together and leveraging advanced automation, these teams can ensure that software not only meets functional requirements but also adheres to the highest security standards.
The Future of Software Supply Chain Security
As technology continues to advance, the landscape of software supply chain security will inevitably evolve. Organizations must recognize that the security threats they face today will not be the same as those they encounter in the future. Therefore, a forward-thinking approach to supply chain security is essential, incorporating emerging technologies and best practices to stay ahead of potential threats.
Looking ahead, the integration of artificial intelligence and machine learning into security frameworks is likely to play a pivotal role in the future of software supply chain security. These technologies can enhance threat detection capabilities and streamline response efforts, ultimately making software development processes more secure. Companies that prioritize innovation in their security practices will be better positioned to navigate the complexities of the software landscape while safeguarding their critical assets.
Frequently Asked Questions
What are the key software security threats impacting the software supply chain?
The key software security threats impacting the software supply chain include Common Vulnerabilities and Exposures (CVEs), malicious packages, exposure of secrets like tokens, and human errors leading to misconfigurations. These factors contribute to vulnerabilities that can jeopardize the integrity and safety of software releases.
How do emerging DevOps risks affect software supply chain security?
Emerging DevOps risks, such as the reliance on manual processes for managing secure ML models, increase the potential for oversights and vulnerabilities in the software supply chain. Organizations must automate their toolchains to mitigate these risks and enhance governance and security.
What are the AI security concerns related to the software supply chain?
AI security concerns related to the software supply chain involve the adoption of public ML models without stringent security controls. With a significant percentage of organizations still using manual validation methods, there is an elevated risk of exposing unverified ML models that may contain security vulnerabilities.
Why is automating toolchains important for software supply chain security?
Automating toolchains is crucial for software supply chain security because it reduces the risk of human error, enhances consistency in security checks, and enables organizations to respond quickly to vulnerabilities in an increasingly complex threat landscape.
How can organizations improve their response to software vulnerabilities?
Organizations can improve their response to software vulnerabilities by conducting regular security scans at both code and binary levels, automating vulnerability management processes, and maintaining updated lists of certified ML models to ensure that only secure components are used in the software supply chain.
What measures should companies implement to secure the software supply chain against CVEs?
To secure the software supply chain against CVEs, companies should implement continuous monitoring of dependencies, conduct thorough security audits of their software and binary levels, and keep track of new vulnerabilities and their severity ratings to prioritize their remediation efforts.
How has the increase in CVEs impacted software supply chain security in 2023?
The increase of 27% in CVEs in 2023 has heightened concerns for software supply chain security, as many of these vulnerabilities may be mis-scored. Organizations must adapt by reviewing their risk assessments and ensuring rigorous testing and validation of software components to address these vulnerabilities.
What best practices can organizations follow to manage software supply chain security?
Best practices for managing software supply chain security include automating security processes, regularly assessing third-party libraries and dependencies, implementing access controls for secure ML model usage, and training teams on identifying and mitigating software security threats effectively.
| Key Point | Details |
|---|---|
| Importance of Software Supply Chain Security | Managing and securing the software supply chain end-to-end is essential for delivering trusted software releases. |
| Emerging Threats and Risks | The JFrog report highlights new software security threats, evolving DevOps risks, and AI-related security concerns. |
| Manual Management Issues | Over a third of organizations rely on manual efforts to manage secure model access, leading to potential oversights. |
| Current Security Practices | Only 43% of IT professionals report conducting security scans at code and binary levels, down from 56% last year. |
| Vulnerability in CVEs | A 27% increase in new CVEs over 2023 indicates rising security vulnerabilities, with many being mis-scored. |
Summary
Software supply chain security is increasingly critical in today’s digital landscape. With the emergence of new threats and risks, organizations must prioritize the management and safeguarding of their software supply chains to deliver trusted software. The recent JFrog report emphasizes the growing complexity of these threats, urging companies to automate their security processes and reduce reliance on manual management practices. Companies adopting AI should focus on implementing AI-ready solutions that enhance security and promote agility. Ensuring robust software supply chain security will help organizations mitigate risks and maintain trust with their stakeholders.