Lookalike domains have emerged as a significant cybersecurity threat, skillfully designed to imitate authentic websites and mislead users. These deceptive domains enable cybercriminals to execute a variety of malicious activities, including phishing scams, domain spoofing, and email fraud. By crafting emails that appear to come from trustworthy sources, attackers exploit the unsuspecting nature of their targets, often leading to dire financial consequences. A recent BlueVoyant report sheds light on the increasing registration of lookalike domains, emphasizing their growing prevalence across diverse industries such as finance and insurance. This alarming trend underscores the urgent necessity for robust cybersecurity measures and heightened awareness among individuals and businesses alike to counteract these dangerous tactics.
Also referred to as fraudulent or imitation domains, lookalike domains replicate genuine web addresses to trick users into clicking on them. These domains are often utilized in social engineering schemes where the intent is to deceive individuals into divulging sensitive information or making fraudulent payments. The similarities in appearance, such as character substitutions and minor adjustments, make it challenging for unsuspecting recipients to recognize these domains as threats. As the landscape of online fraud continues to evolve, the importance of recognizing and mitigating these hazards cannot be overstated. Staying informed about the tactics associated with domain impersonation serves as a vital first line of defense against the increasing prevalence of such online scams.
What Are Lookalike Domains and How Do They Work?
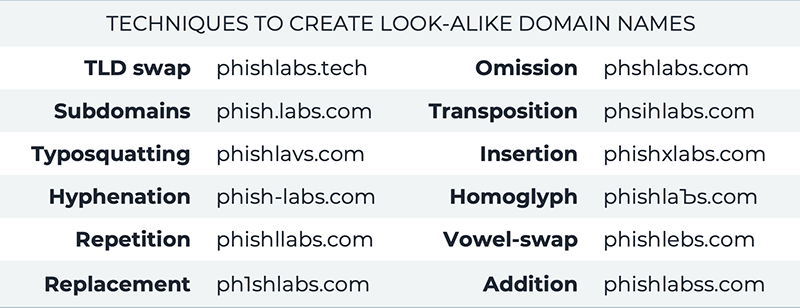
Lookalike domains are fraudulent web addresses that closely resemble legitimate ones, making them an effective tool for cybercriminals. By altering a few characters, such as replacing similar-looking letters or adding extra words, attackers create domains that can easily confuse unsuspecting users. These domains play a pivotal role in various malicious activities, particularly phishing scams, where individuals are tricked into providing sensitive information such as login credentials or financial details. The ease with which these domains can be registered and the sophistication of their designs pose significant risks to both individuals and organizations.
In many cases, lookalike domains can deceive even the most vigilant users, especially when they are designed to mimic trusted brands. Cybercriminals often target sectors dealing with sensitive information, such as finance and insurance, where the stakes are high. The effectiveness of these deceptive tactics highlights the importance of understanding how lookalike domains operate and the necessity for proactive countermeasures to protect against phishing and social engineering attacks.
The Growing Threat of Lookalike Domains in Cybersecurity
The rise of lookalike domains is a significant trend that raises alarms within the cybersecurity community. A recent report by BlueVoyant reveals that these domains have seen a sharp increase in registrations, which correlates with the high volume of phishing scams reported across various industries. Attackers leverage these domains to send emails that appear trustworthy, thereby tricking recipients into clicking links or downloading malware. As criminals become more sophisticated, understanding the evolving nature of lookalike domains is crucial for cybersecurity professionals and organizations alike.
The impact of lookalike domains extends beyond individual users; entire industries, including construction and legal sectors, face heightened risks from these malicious entities. Addressing this growing threat requires not only awareness but also the implementation of comprehensive security measures. Businesses must invest in advanced technologies that can detect subtle variations in domain names and enhance their overall email security protocols to reduce the risk of falling victim to email fraud.
Detecting and Mitigating Lookalike Domain Threats
Detecting lookalike domains poses a complex challenge due to the sheer volume of potential threats and the subtlety with which they can be created. Tools utilizing string similarity models play a significant role in identifying these domains by evaluating how closely they resemble legitimate URLs. This technology allows cybersecurity teams to pinpoint potentially harmful domains before they can execute phishing campaigns. Continuous monitoring and assessment are vital in maintaining an adaptive defense against the emergence of new lookalike domains.
Moreover, organizations must establish protocols for rapid response and remedial action when a lookalike domain is identified. This could include working with domain registrars to take down fraudulent websites promptly or alerting clients about potential threats through effective communication and education. Collaborative efforts across various sectors are essential to combat the fraudulent tactics employed by cybercriminals, ensuring a united front against evolving domain-spoofing strategies.
The Role of Social Engineering in Lookalike Domain Scams
Social engineering techniques are central to the effectiveness of lookalike domain scams, as they exploit human psychology and trust to perpetrate fraud. Cybercriminals craft emails that appear legitimate, often using social engineering tactics such as urgency or fear to compel individuals to act quickly without verifying the authenticity of the request. This manipulation of emotional responses makes it easier for attackers to trick victims into disclosing sensitive information or clicking on malicious links.
To combat social engineering attacks related to lookalike domains, ongoing education and awareness training for employees and users are crucial. Organizations should cultivate a culture of skepticism, encouraging individuals to verify suspicious communications and messages. Implementing security measures, such as multi-factor authentication and domain whitelisting, can further help in reducing the risk that arises from social engineering tactics.
The Financial Impact of Lookalike Domains on Businesses
The financial repercussions of lookalike domains can be staggering for businesses, as cybercriminals utilize these deceptive addresses to commit fraud, resulting in significant financial losses. Whether it is through successful phishing scams that lead to direct theft of funds or the long-term damage to a company’s reputation, the impact is far-reaching. Organizations can find themselves facing legal challenges, not to mention the costs associated with recovery and breach response efforts.
Mitigating these risks requires strategic investments in cybersecurity and employee training. By employing advanced technologies for monitoring and detecting lookalike domains, businesses can protect themselves and their customers from falling victim to cyber fraud. Additionally, developing comprehensive incident response plans helps organizations respond rapidly to potential breaches, minimizing the financial impact of such attacks.
Case Studies: Real-Life Examples of Lookalike Domain Attacks
Examining case studies of lookalike domain attacks provides valuable insights into how these scams unfold and the tactics used by cybercriminals. For instance, in 2020, a high-profile attack targeted a leading financial institution using a lookalike domain that mimicked their official website. Customers received numerous phishing emails that requested updates to their account information, resulting in thousands of compromised accounts before the attack was mitigated. Such incidents underscore the necessity for companies to remain vigilant against the threats posed by lookalike domains.
Another notable case involved a legal firm that experienced an influx of fraudulent invoices sent from a lookalike domain. Due to the convincing design and timely delivery of these emails, several clients inadvertently processed payments to the scammers. This incident emphasizes the importance of implementing more robust verification processes and educating clients about recognizing fraudulent requests. Understanding these real-life scenarios is crucial for organizations to devise better strategies to combat similar attacks in the future.
Emerging Technologies in the Fight Against Lookalike Domains
As the threat landscape evolves, so too must the technologies used to combat cybersecurity threats like lookalike domains. Innovations such as machine learning algorithms are increasingly being adopted to identify and flag potential fraudulent domains based on behavioral analysis and historical data. By training these systems to recognize patterns indicative of lookalike domains, organizations can vastly improve their chances of intercepting cyber attacks before they can cause harm.
Furthermore, advancements in artificial intelligence are enhancing the capability to conduct real-time monitoring of newly registered domains. These technologies can provide alerts to cybersecurity teams when potential lookalike domains surface, ensuring timely responses to Fast-Track evolving threats. Investing in such technologies represents a proactive approach to ensure stronger defenses against the prevalent issue of email fraud and domain spoofing.
Best Practices for Protecting Against Lookalike Domain Attacks
To mitigate the risks associated with lookalike domains, organizations need to adopt best practices focused on both prevention and detection. Firstly, implementing strict domain registration processes, including registering common misspellings and variations of their domain names, can significantly decrease the likelihood of impersonation. Additionally, organizations should educate employees and clients on the importance of verifying the source of communications, particularly when sensitive information is requested.
Employing comprehensive email security solutions that include advanced spam filters and anti-phishing tools can help minimize the chances of malicious emails reaching their intended targets. Conducting regular security audits and penetration testing can also uncover potential vulnerabilities within an organization’s defenses. By teaching best practices and implementing proactive measures, businesses can bolster their defenses against deceptive tactics utilized by cybercriminals.
The Importance of Collaboration in Cybersecurity
To effectively counter the growing threat of lookalike domains, collaboration among various stakeholders is essential. Government agencies, private sector organizations, and cybersecurity firms must work together to share information and intelligence on emerging threats. Developing partnerships enables a broader understanding of tactics used by cybercriminals and facilitates the pooling of resources for addressing these threats in a coordinated manner.
Moreover, collaborative efforts can aid in standardizing protocols for reporting and taking down fraudulent domains. Establishing industry-wide initiatives can enhance awareness of lookalike domain risks and encourage the sharing of best practices. By working collectively, industries can build a more robust defense against the increasingly sophisticated tactics employed by those looking to exploit vulnerabilities in cybersecurity.
Frequently Asked Questions
What are lookalike domains and how do they relate to phishing scams?
Lookalike domains are web addresses that closely mimic legitimate domains, often using similar characters or slight variations. Cybercriminals utilize these domains to conduct phishing scams, deceiving users into believing they are interacting with a trusted source. This tactic greatly enhances the likelihood of successful scams because victims are more likely to click links that appear legitimate.
How can businesses protect themselves against domain spoofing using lookalike domains?
To guard against domain spoofing via lookalike domains, businesses should implement strong cybersecurity measures such as regularly monitoring domain registrations, utilizing advanced detection tools, and educating employees about social engineering tactics. Regular audits of email communications can also help identify possible email fraud linked to lookalike domains.
What are some common tactics used in lookalike domain schemes?
Attackers use various tactics in lookalike domain schemes, including substituting visually similar characters (like ‘0’ for ‘o’), rearranging letters, or using keywords associated with well-known brands. These strategies exploit human error and increase the chance of domain recognition, which can lead to successful phishing or social engineering attacks.
What impact do lookalike domains have on cybersecurity efforts?
Lookalike domains significantly challenge cybersecurity efforts by complicating the detection of fraudulent activities. The rise of these deceptive domains requires businesses to adopt continuous monitoring and advanced detection techniques to identify and mitigate the risks associated with phishing scams and email fraud effectively.
Why is vigilance important in combating lookalike domains?
Vigilance is critical in combating lookalike domains because these fraudulent sites can swiftly emerge and entice unsuspecting users. With the increasing sophistication of social engineering tactics, ongoing awareness and proactive measures are necessary to identify threats early and protect personal and organizational information from cybercriminals.
What tools can help detect lookalike domains before they become a threat?
To detect lookalike domains before they pose a threat, organizations can utilize string similarity models and automated monitoring systems. These tools analyze domain registrations to assess how closely they match legitimate domains, allowing for the identification of potentially malicious domains that may have been overlooked.
How do social engineering tactics relate to lookalike domains in cyberattacks?
Social engineering tactics often accompany lookalike domains in cyberattacks, as attackers aim to manipulate victims into providing sensitive information or clicking malicious links. By leveraging familiar branding or deceptive email structures, these tactics exploit the psychological trust people place in recognized entities, enhancing the chances of successful fraud.
What industries are most affected by the rise of lookalike domains?
The rise of lookalike domains impacts various sectors, notably finance, insurance, construction, and legal industries. These sectors are often targeted due to their sensitive nature and the trust users place in their communications, making them prime candidates for phishing scams and email fraud.
| Key Points |
|---|
| Lookalike domains mimic authentic domains for fraudulent purposes. |
| They facilitate various scams, including phishing and invoice fraud. |
| Cybercriminals lure victims through emails that appear to come from trusted sources. |
| The rise in lookalike domains poses risks across multiple sectors. |
| Identifying lookalike domains is challenging due to similar naming conventions. |
| Advanced detection models are necessary for recognizing subtle domain variations. |
| Continuous monitoring is crucial to mitigate fraud risks associated with these domains. |
Summary
Lookalike domains are a growing concern that threaten the security of individuals and businesses alike. These domains, which closely resemble genuine ones, are setting the stage for a variety of scams, including phishing and social engineering attacks. With the prevalence of lookalike domains on the rise, it is essential for companies in all industries to implement robust security measures and maintain vigilant monitoring. The deceptive tactics employed by cybercriminals highlight the urgent need for collaborative efforts to enhance detection capabilities and mitigate the risks associated with these fraudulent domains.